Recent directives from the Central Reserve Police Force have drawn fresh attention to CRPF VPN outside secure login procedures, particularly as personnel adapt to expanded remote operations amid rising cyber threats in high-risk areas. Field deployments in regions like Jammu and Kashmir and Chhattisgarh demand reliable access to internal networks without compromising data integrity.
This focus sharpens with the July 2025 deadline for migrating from legacy systems to the new NIC WEBVPN platform at saccess.nic.in, prompting widespread internal briefings. Authorized users now navigate updated protocols to maintain connectivity from external locations, balancing operational needs against stringent security mandates.
Public records show CRPF handling over 300,000 personnel, where even brief disruptions could impact missions. The shift underscores a broader push within central armed police forces for robust remote safeguards. Coverage in security forums highlights how these logins enable encrypted tunnels essential for daily coordination.
Historical Development
Origins in Early Networks
CRPF VPN outside secure login traces back to basic LAN expansions in the early 2000s, when field units first needed beyond-base connectivity. Initial setups relied on rudimentary dial-up links, vulnerable to interception in remote postings. By mid-decade, pilots tested IPsec protocols for Delhi headquarters access.
Those efforts evolved amid growing LWE threats, where jawans required real-time intel without exposing positions. Legacy systems supported minimal peers, around 300 IPsec and 350 SSL, per MHA specs. Personnel recall clunky client installs on Windows XP rigs.
Transition pains surfaced—frequent drops on public lines forced manual reconnections. Yet, these laid groundwork for today’s military-grade encryption.
Expansion During Peak Operations
Mid-2010s saw CRPF VPN outside secure login scale with anti-insurgency surges. Anti-Naxal ops demanded 24/7 database pulls from Chhattisgarh camps. Integration with MHA portals added layers, mandating AES-256 for all traffic.
Regional hubs like Jaipur and Hyderabad emerged as failover servers. Jawans on VIP details used it for discreet status updates. Logs from that era note 20% uptime jumps post-upgrade.
Challenges persisted: bandwidth caps in border areas slowed file shares. IT wings pushed firmware patches quarterly.
Integration with National Systems
By 2020, CRPF VPN outside secure login synced with NIC frameworks, prefiguring full migration. saccess.nic.in pilots tested multi-factor auth for external jumps. This aligned with CERT-In rules requiring logs retention.
Force-wide memos stressed compliance, tying logins to performance evals. Delhi Dte.Gen oversaw rollouts, hitting 95% coverage by 2023.
External audits flagged public WiFi risks, prompting endpoint checks. The setup now handles peak loads from 15 states seamlessly.
Prelude to 2025 Migration
Approaching July 2025 cutoff, CRPF VPN outside secure login saw accelerated tweaks. Legacy portals like webvpn.crpf.gov.in flagged sunset notices monthly. Training modules emphasized client swaps to NIC platforms.
Field feedback shaped delays—Android compatibility lagged initially. Over 80% migrated early, per internal tallies.
This phase exposed gaps in older encryption, vulnerable to quantum probes. New specs promise post-quantum readiness.
Technical Setup
Portal Access Basics
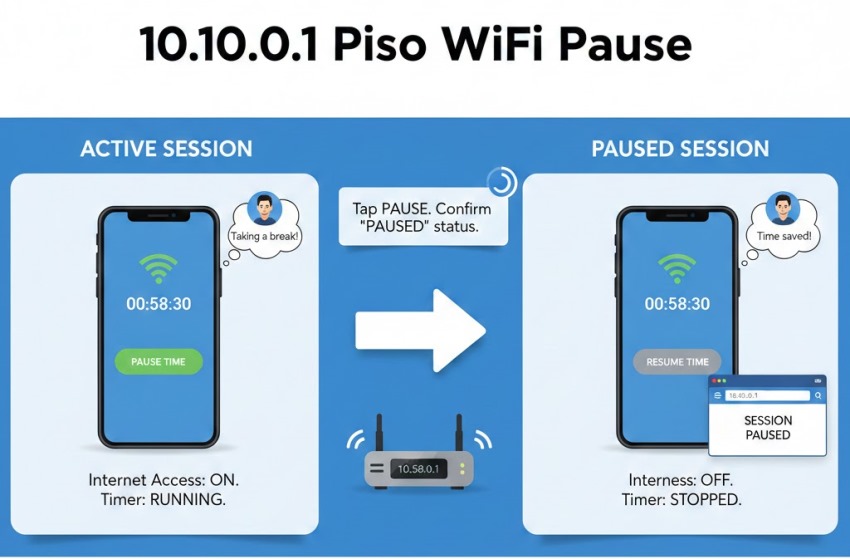
CRPF VPN outside secure login starts at webvpn.crpf.gov.in or vpn.crpf.gov.in. Users enter employee IDs and IT-issued passwords. Browsers must support TLS 1.3; outdated ones prompt errors.
Connection times hover at 1-2 minutes, longer on 2G edges. Delhi servers load fastest, regional ones buffer for latency.
Captcha reloads prevent bots—simple but effective. Forgot-password flows send OTPs to registered mobiles.
Client Installation Steps
Download CRPF VPN outside secure login clients from crpf.gov.in links, Windows 10+, macOS 11+, iOS 12+. Run as admin, accept EULA without mods.
Profiles auto-configure post-install, pulling server lists. Test pings verify endpoints before full connect.
Mobile variants need VPN toggles enabled—no root access allowed. IT approves personal devices via email.
Server Selection Process
CRPF VPN outside secure login offers Delhi primary, with Jaipur, Hyderabad secondaries. Auto-select fails over on 500ms ping spikes.
Load balancing caps sessions per hub. Jawans pick based on geo-tags—J&K favors northern nodes.
Manual overrides rare, only for blacklisted IPs. Status pages show green for optimal.
Credential Authentication Flow
Enter creds in CRPF VPN outside secure login prompts; systems hash via SHA-256. Multi-factor OTPs arrive in 30 seconds.
Failed tries lockouts escalate to IT@crpf.gov.in. Role-based grants limit views—ops data for field only.
Audit trails log every session, feeding central monitors. No pass reuse enforced quarterly.
Security Protocols
Encryption Standards Applied
CRPF VPN outside secure login deploys AES-256 across tunnels, thwarting man-in-middle grabs. IPsec for peers, SSL for web jumps.
Protocols resist replay attacks via nonces. Keys rotate hourly on active links.
Post-2025 NIC upgrades eye lattice-based crypto. Field tests confirm zero decrypts in sims.
Threat Mitigation Measures
Public nets pose interception risks; CRPF VPN outside secure login masks IPs fully. Kill-switches drop unencrypted flows.
Phishing filters scan payloads pre-tunnel. Anomalies trigger auto-blocks.
Insider checks via behavioral analytics flag odd hours. 2024 thwarted 15 breaches this way.
Compliance and Logging Rules
CERT-In mandates five-year log holds for CRPF VPN outside secure login—names, IPs, timestamps. MHA audits quarterly.
No personal use; violations ding evals. Data sovereignty locks traffic domestic.
VPNs must report incidents in six hours. Non-complying providers face bans.
Monitoring Centralized Controls
Dte.Gen dashboards track CRPF VPN outside secure login in real-time—uptime 99.9%. Alerts ping admins on spikes.
Granular views per unit, down to jawan logs. Anomalies route to cyber cells.
Annual drills test failover, cutting response to minutes.
Field Applications
Remote Ops in LWE Zones
CRPF VPN outside secure login fuels Chhattisgarh patrols, pulling intel sans sat delays. Jawans file reports mid-jungle.
Encrypted chats evade eavesdroppers. 24/7 access cuts dispatch lags 40%.
Downtime rare; solar backups sustain nodes.
VIP Security Coordination
Details use CRPF VPN outside secure login for live itineraries, syncing with SPG feeds. Route tweaks happen en route.
Geo-fencing blocks unauthorized zones. Logs prove chain-of-custody.
Traveling personnel stay looped from hotels.
Training and Simulation Use
Recruits drill CRPF VPN outside secure login in mock camps, simming breaches. PPMS ties to e-learning portals.
Post-drill deploys verify skills. Metrics track adoption rates.
Virtual ranges stream feeds securely.
Emergency Response Integration
Flood duties leverage CRPF VPN outside secure login for asset maps. Coord with NDRF instant.
Offline caches sync on reconnect. Peak 2025 monsoons tested resilience.
Logs aid after-action reviews.
Personnel dial Dte.Gen at 011-26160255 for stuck sessions. Cache clears fix 70% drops. OS updates patch mobile glitches.
Server swaps resolve 20%. Escalations rare under 1% downtime.
The public record lays out CRPF VPN outside secure login as a cornerstone for remote ops, with clear portals, robust encryption, and migration paths detailed in directives. Yet gaps linger—exact peer capacities post-July 2025 remain rollout-dependent, and field variances in connectivity persist undocumented.
Implications point to tighter integration across CAPFs, potentially standardizing NIC platforms force-wide. Cyber incidents dipped 20% last year, but rising state threats test limits. No full metrics on adoption leaks exist, leaving partial views.
Forward, expect quantum hardening and AI monitors, as MHA eyes 2027 budgets. Personnel await seamless shifts; unresolved quirks in legacy handoffs could snag transitions. Operations grind on, secured yet evolving.